Network Security
Important
Petabridge.Cmd does not ship with any form of out-of-the-box authentication or encryption. It's on the roadmap but in the meantime please take care to secure the zone through which you use Petabridge.Cmd at the network level. We include some instructions for doing this below.
Petabridge.Cmd in a Secure Zone
In general, one of the recommended techniques to protect any type of socket-based application is to place it within a secure zone. Everything from database servers to high frequency trading systems can be protected this way.
In Windows Azure this is a Virtual Network; in Amazon Web Services this is a Virtual Private Cloud.
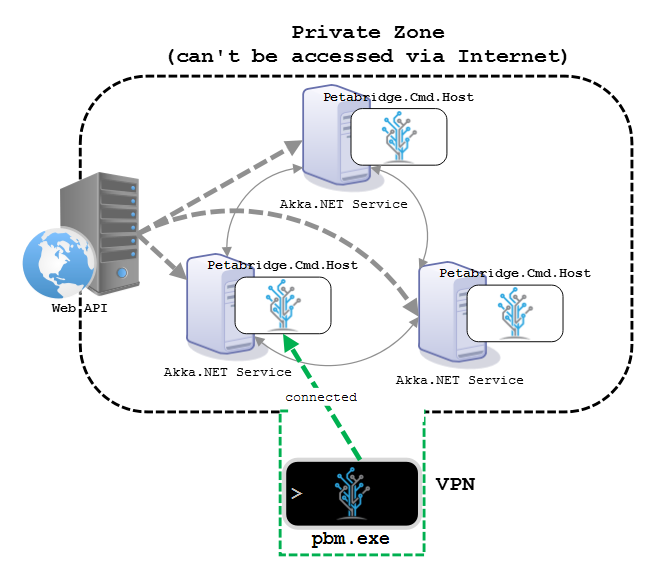
In all other environments a secure zone is created through putting all of the internal services into a private network and only allowing communication to those services to occur through a whitelisted set of endpoints that also reside on a public network of some kind.
Petabridge recommends keeping Petabridge.Cmd endpoints limited to the private network zone only.

This is a good practice many Akka.NET users are already using for Akka.Remote and Akka.Cluster, so it's not something unique to Petabridge.Cmd.
If you need to access Petabridge.Cmd from a work station or any other type of machine residing somewhere other than the private zone, we recommend using a Virtual Private Network for this, as such: